Effective cyber security requires the balancing of three elements:
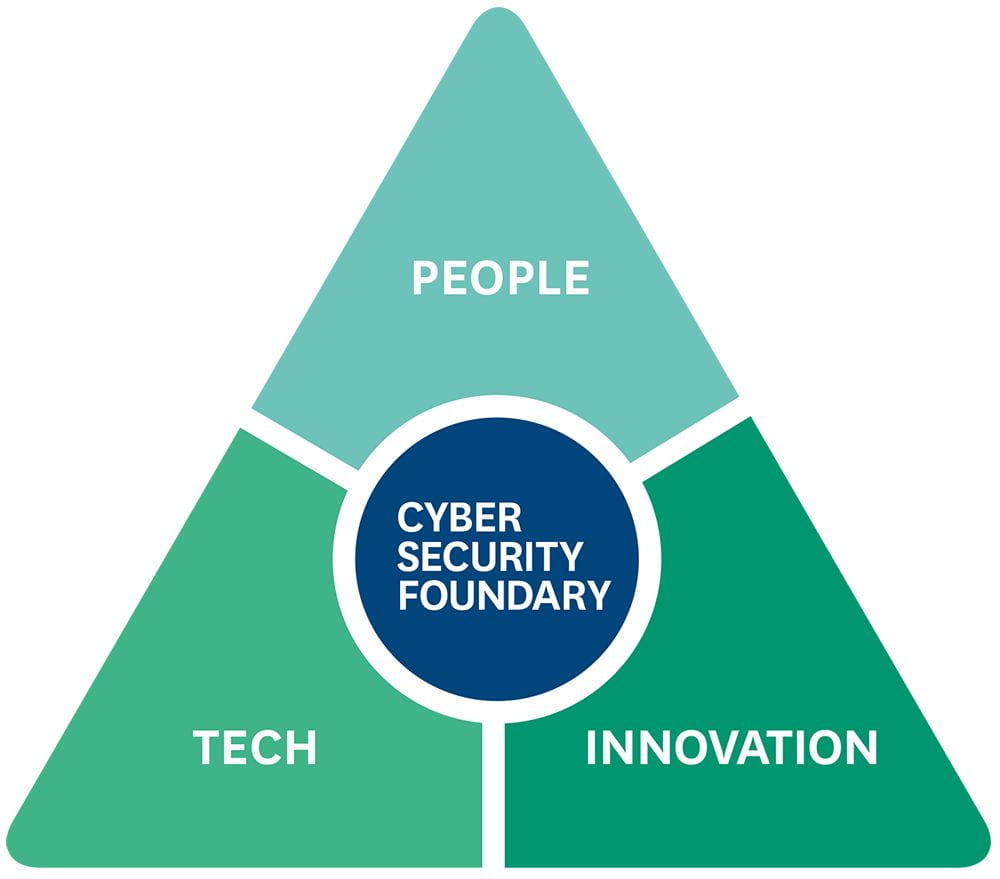
People
Large organisations may have a diverse workforce with limited technical skills. Security is only as strong as the weakest link. The Cyber Security Foundry’s expertise in Human-Centric Security and Cyber Security Psychology can support you in developing systems to help employees be more focused and resilient against social engineering attacks.
Tech
The Cyber Security Foundry includes experts in Computer Science and Engineering who are developing next-generation technology.
- The Cloud has changed the way organisations manage and store their data. Standard encryption can protect the data when at rest or transferred across the network. However, processing requires the data to be decrypted – and this is when attackers can strike. Our experts in Functional Encryption have developed advanced encryption technology that allows the data to be processed even when it is encrypted, meaning your data is always protected.
- The introduction of Internet of Things (IoT) devices is creating new and exciting opportunities for Smart Cities and Industry 4.0. However, these devices increase the attack surface and create new entry points for attackers. Our experts in IoT and Electrical Engineering can help identify attack entry points and defend against cyber attacks targeting IoT devices.
Innovation
The Cyber Security Foundry is driving the development of new ideas and tools for the next generation of security systems.
- The rise of data protection regulations, and expectations by individuals, is driving the development and use of privacy-preserving tools for handling data, such as privacy-preserving analytics and contact tracing. The cryptographic expertise at the Cyber Security Foundry can advise and review privacy-preserving solutions in these areas.
- Distributed Ledger Technology is disrupting the business models of many well-established institutions, such as banks and law firms. Our experts in blockchain and decentralised systems are well-placed to help you understand this technology, and its opportunities and risks.

